Idempotency is a reliable way of building robust API, particularly in distributed systems where retries and network failures are common. This blog explores the concept of idempotency and multiple ways to implement it using a Spring Boot file upload service, ensuring no duplicate uploads occur.
What You’ll Learn
- The Concept of Idempotency and why it matters in API design.
- Different Approaches to Implementing Idempotency in Spring Boot.
- A Practical File Upload Service showcasing these approaches.
- Best Practices, Pitfalls, and Optimization Tips for idempotent APIs.
Key Takeaways
- Idempotency Prevents Duplicates: It ensures reliable APIs, handling retries without creating duplicate files.
- Choose the Right Strategy: Options like Idempotency Keys, Content Hashing, or a combination offer flexibility for various use cases.
- Content Hashing Simplifies Deduplication: Hashing automates duplicate detection but requires more compute for large files.
- Combine for Reliability: Pairing Idempotency Keys with Content Hashing is robust and handles client errors effectively.
- Follow Best Practices: Use strong hashing algorithms, set expiration for keys, and test thoroughly to build resilient APIs.
Apply these principles to create efficient, user-friendly, and reliable file upload services.
The Problem: Why Idempotency Matters in File Uploads
Imagine a scenario where a user uploads a file to your server, but due to network issues, they retry the same request multiple times. Without idempotency, your server might save the same file multiple times, leading to:
- Wasted Storage: Duplicate files unnecessarily consume storage.
- Inconsistent State: Multiple records for the same file can cause confusion.
- User Frustration: Users might see duplicate entries in their file history.
To address this, an idempotent API ensures that repeated uploads of the same file result in only one stored copy.
Approaches to Implementing Idempotency in Spring Boot
Here are four different strategies to implement idempotency for a file upload service in Spring Boot:
1. Idempotency Key-Based Deduplication
How It Works:
- Clients include a unique
X-Idempotency-Keyheader with each request. - The server stores this key alongside the uploaded file’s metadata.
- If a request with the same key is received again, the server returns the already-stored file’s response instead of reprocessing the upload.
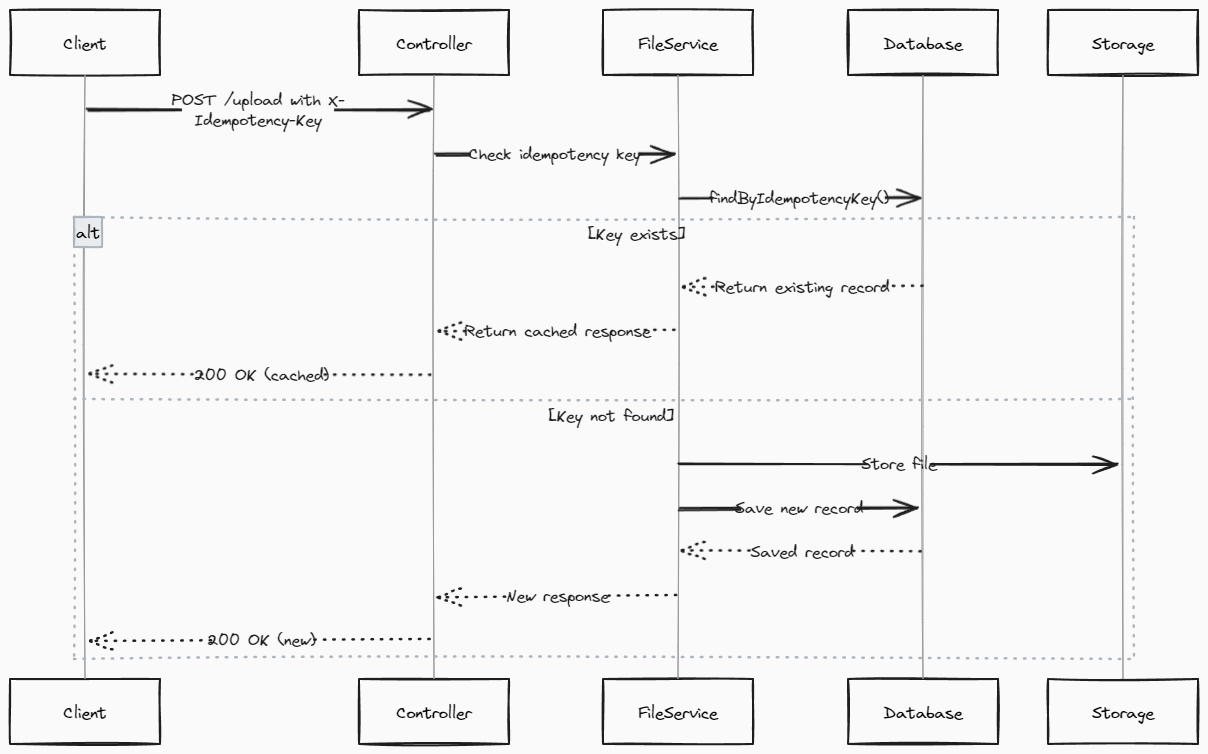
Implementation Steps:
- Store the
idempotencyKeyin a database table. - Before processing a new upload, check if the key already exists.
- If the key exists, return the corresponding file metadata.
Code Example:
| |
Pros:
- Simple and effective.
- Works well in systems where clients can reliably generate unique keys.
Cons:
- Relies on client cooperation to generate unique keys.
- Requires storage and lookup of keys on the server side.
2. Content Hashing for Deduplication
How It Works:
- The server generates a hash (e.g., MD5 or SHA-256) of the file content.
- Before saving the file, the server checks if a file with the same hash already exists.
- If a match is found, the server rejects the upload or returns the existing file’s metadata.
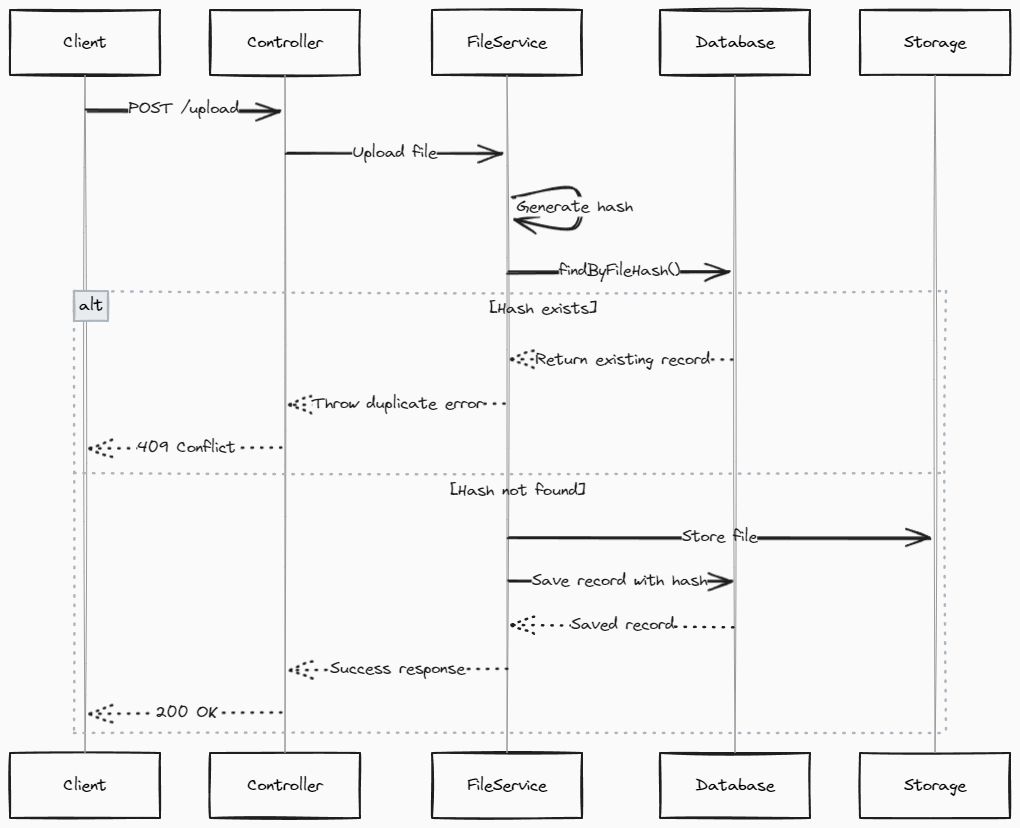
Implementation Steps:
- Generate a hash of the file’s content.
- Store the hash in the database alongside the file metadata.
- Check for hash collisions before processing new uploads.
Code Example:
| |
Pros:
- Automatic deduplication based on file content.
- No reliance on client behavior.
Cons:
- Computational overhead for hashing large files.
- Collisions are rare but theoretically possible (depending on the hashing algorithm).
3. Combination of Idempotency Key and Content Hash
How It Works:
- Combines the strengths of both strategies.
- Clients provide an
X-Idempotency-Key, but the server also validates file uniqueness using content hashing.
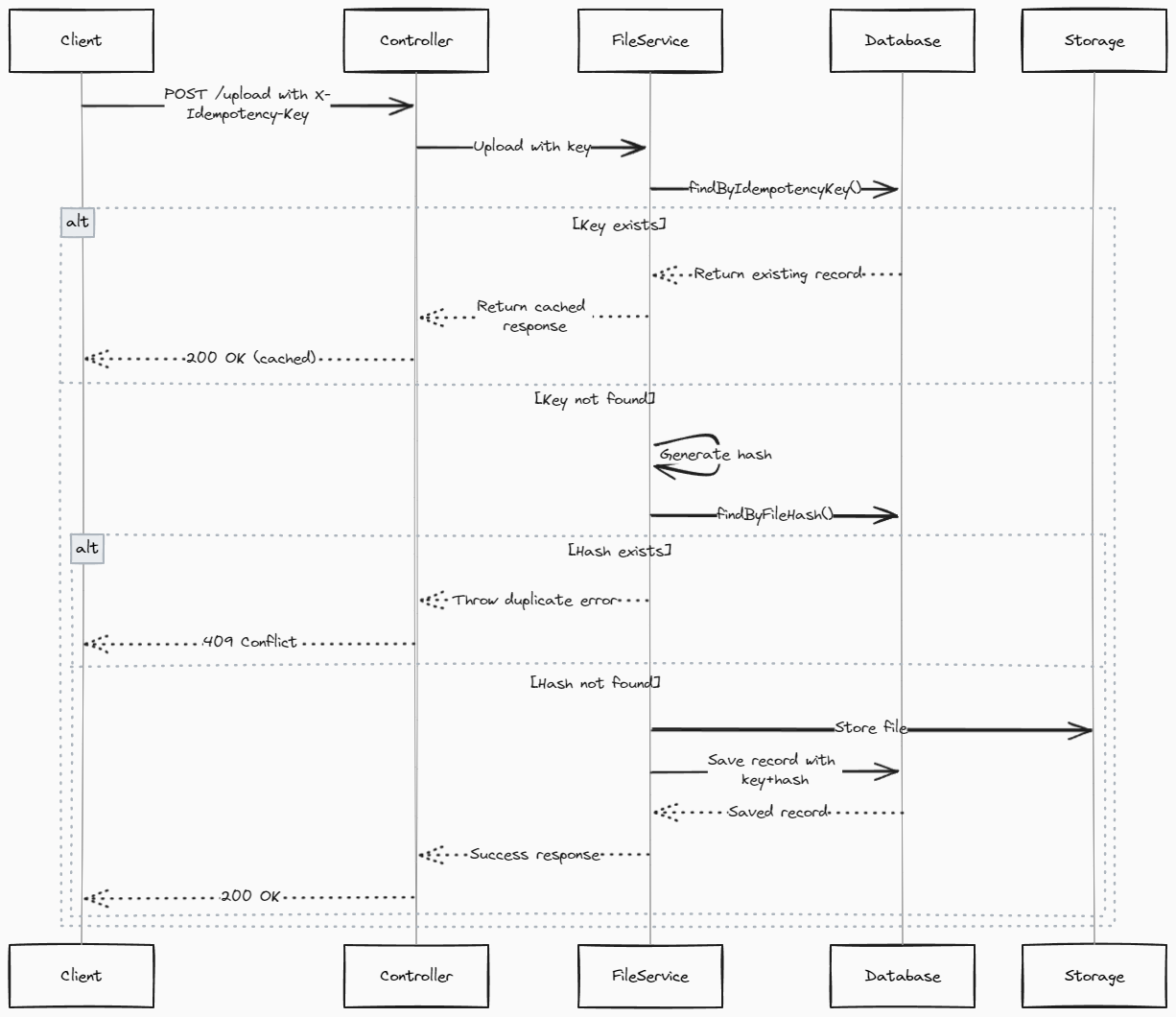
Implementation Steps:
- Check for the
idempotencyKeyin the database. - If not found, compute the file hash and check for duplicates.
- Save both the
idempotencyKeyand file hash in the database.
Code Example:
| |
Pros:
- Robust against client errors (e.g., duplicate idempotency keys).
- Guarantees no duplicate files.
Cons:
- Adds complexity and slightly more overhead.
4. Token-Based Deduplication
How It Works:
- After a successful upload, the server issues a token (e.g., a UUID or file hash).
- Clients must include this token in subsequent uploads to reference the original file.
- If the token is valid, the server skips the upload and returns the original file’s response.
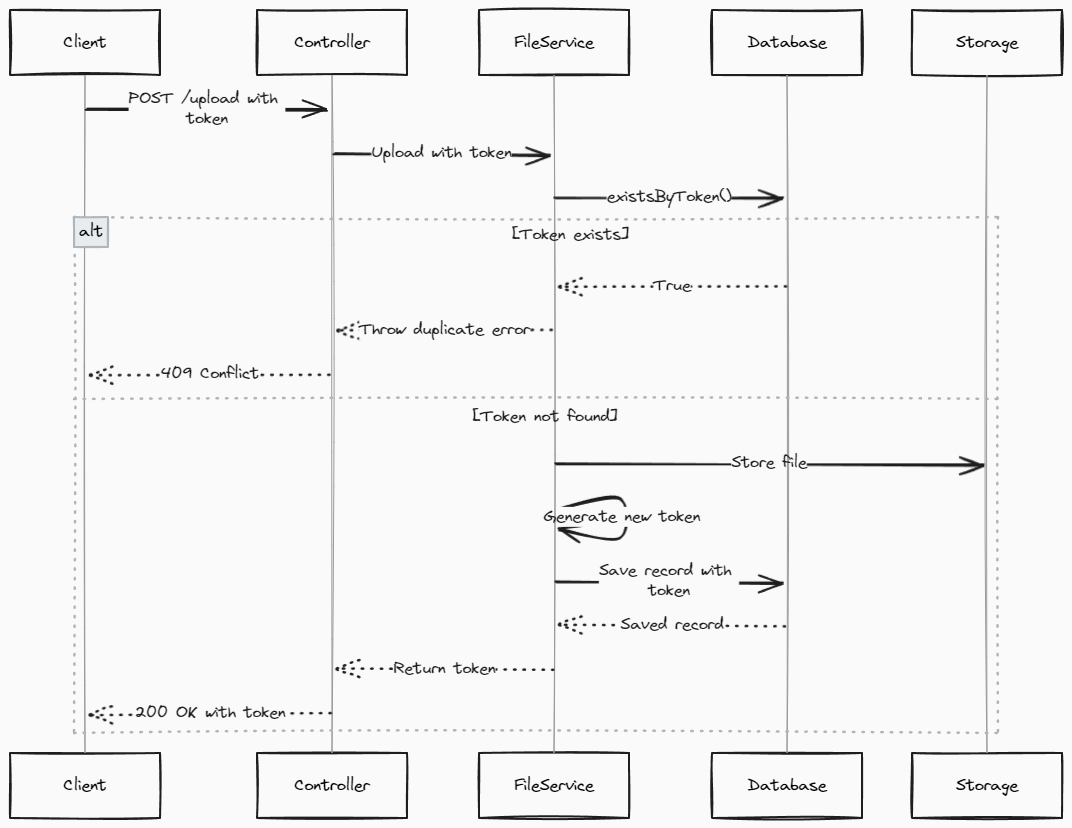
Implementation Steps:
- Generate a token after the first successful upload.
- Store the token alongside the file metadata.
- Require clients to include the token in subsequent requests.
Code Example:
| |
Pros:
- Offloads responsibility for deduplication to the client.
- Reduces server-side storage requirements for idempotency keys.
Cons:
- Potentially less user-friendly, as clients must manage tokens.
Choosing the Right Approach
The best strategy depends on your application’s requirements:
| Criteria | Idempotency Key | Content Hash | Key + Hash | Token |
|---|---|---|---|---|
| Client Cooperation Needed | Yes | No | Partial | Yes |
| Storage Efficiency | Moderate | High | Moderate | High |
| Computational Overhead | Low | Medium | Medium | Low |
| Robustness Against Duplicates | Moderate | High | High | High |
Best Practices for Idempotent File Uploads
- Use Strong Hashing Algorithms: Prefer SHA-256 over MD5 for better collision resistance.
- Set Expiry for Idempotency Keys: To avoid unbounded growth in storage, set a TTL (time-to-live) for keys.
- Test for Edge Cases: Simulate network failures and retries during testing.
- Provide Clear Error Messages: Inform clients why a request was rejected (e.g., duplicate file detected).
Conclusion
Idempotency is a critical design principle for modern APIs, ensuring consistency and reliability in distributed systems. By carefully choosing an implementation strategy—such as idempotency keys, content hashing, or a combination—you can build robust file upload services that prevent duplicate uploads and enhance user experience.
Next Steps:
- Experiment with the provided code examples.
- Explore additional use cases for idempotency (e.g., payment processing).
- Dive deeper into hashing algorithms and database optimization for production-grade systems.
By implementing idempotency in your Spring Boot applications, you can create resilient and user-friendly services that handle the challenges of distributed systems gracefully.